DDOS attack recent news making rounds is “Attack on the archive of our own AO3 Website“
A distributed denial-of-service (DDoS) attack is an attempt to make a machine or network resource unavailable to its intended users by overwhelming it with traffic.
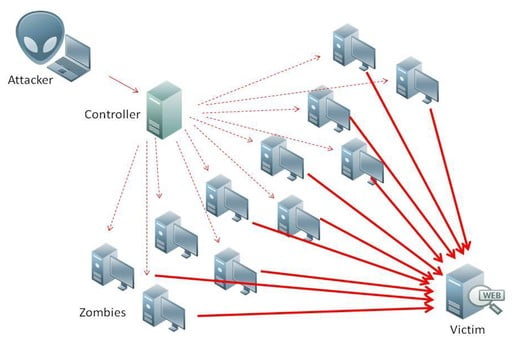
The anatomy of a DDoS attack can be broken down into the following steps:
- The attacker selects a target. This could be a website, a server, or even an entire network.
- The attacker gathers a botnet. A botnet is a network of compromised computers that are controlled by the attacker.
- The attacker directs the botnet to attack the target. This can be done by sending a flood of traffic to the target’s IP address.
- The target is overwhelmed and becomes unavailable. The target’s resources are depleted, and it can no longer handle legitimate traffic.
There are two main types of DDoS attacks:
- Volumetric attacks: These attacks involve sending a large amount of traffic to the target. This can be done by using a botnet or by exploiting a vulnerability in the target’s network.
- Protocol attacks: These attacks exploit vulnerabilities in specific protocols. For example, an attacker could send a flood of SYN packets to a web server, which would prevent the server from responding to legitimate requests.
DDoS attacks can have a significant impact on businesses and organizations. They can disrupt operations, damage reputations, and even lead to financial losses.
Here are some of the telltale signs of a DDoS attack:
- Suspicious amounts of traffic originate from a single IP address or IP range.
- A flood of traffic from users who share a single behavioral profile, such as device type, geolocation, or web browser version.
- A sudden increase in server errors or timeouts.
- A decrease in website performance or availability.
If you suspect that your organization is under attack, it is important to take action immediately. You should contact your hosting provider or security team and implement any mitigation measures that they recommend.
Here are some tips for preventing DDoS attacks:
- Keep your software up to date. Software updates often include security patches that can help to protect your systems from attack.
- Use strong passwords and enable multi-factor authentication. This will make it more difficult for attackers to gain access to your systems.
- Monitor your network traffic for suspicious activity. This will help you to identify and respond to DDoS attacks early on.
- Use a DDoS mitigation service. This can help to protect your systems from even the most sophisticated DDoS attacks.
By following these tips, you can help to protect your organization from DDoS attacks.
Image credit
Nasanbuyn, CC BY-SA 4.0, via Wikimedia Commons